Publisher verification and app consent policies [General Availability]
With usage of cloud apps and the remote work, attackers leverage application-based attacks, such as consent phishing. Indeed, they try to to gain unwarranted access to valuable data in cloud services.
General availability of publisher verification
At the beginning of this month, Microsoft announced that publisher verification was generally available.
This capability allows developers to add a verified identity to their app registrations and demonstrate that the app comes from an authentic source.
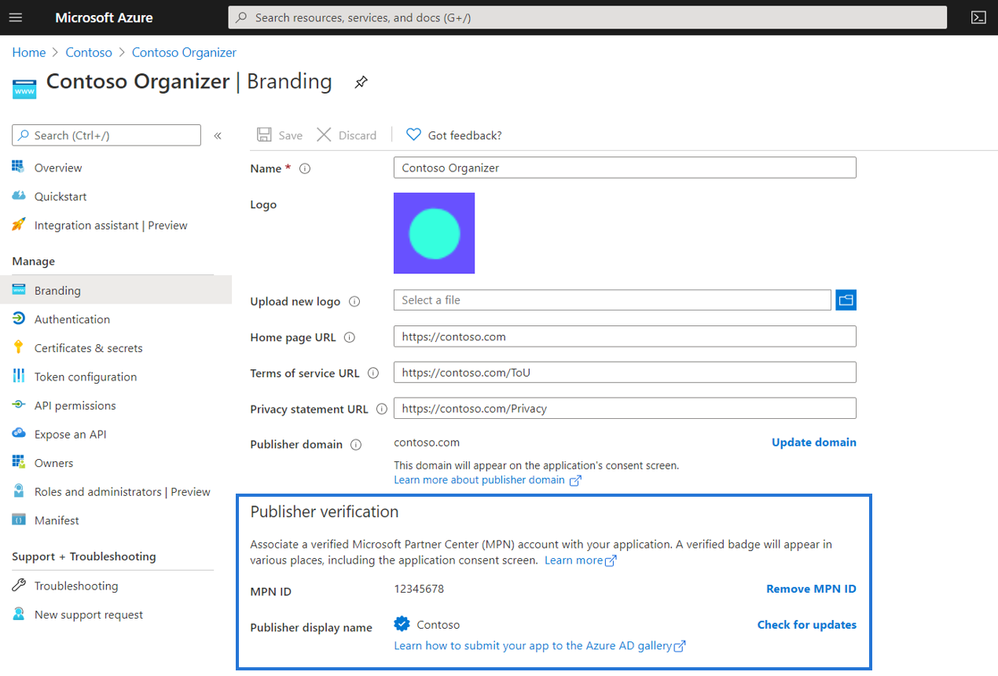
For developers, publisher verification allows them to distinguish their apps to customers by receiving a “verified” badge that appears on the Azure AD consent prompt
Admins can also set user consent policies based on if an apps is publisher verified helping streamline adoption.
User consent updates for unverified publishers
End users will no longer be able to consent to new multi-tenant apps registered after November 8th, 2020 coming from unverified publishers.
These apps may be flagged as risky and will be shown as unverified on the consent screen. Apps requesting basic sign-in and permissions to read user profile will not be affected, nor will apps requesting consent in their own tenants.
To prepare for this change if you are an app developer, add a verified publisher to all your multi-tenant app registrations.
General availability of app consent policies
To help admins control what apps their users can consent to, Microsoft is announcing general availability of the new app policies for end user consent.
With app consent policies, admins have more controls over the apps and permissions to which users can consent.
Customers can manage settings for user consent by choosing from the following built-in app consent policies in the screenshot below:
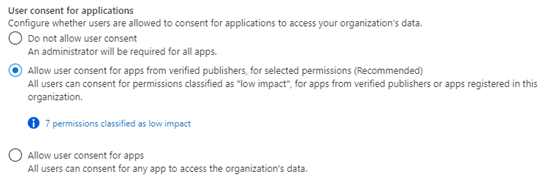
It is recommend that you set the policy to allow user consent for apps from verified publishers and configure the admin consent workflow to streamline access for end users who are not allowed to consent.


No Comments