Web content filtering with Microsoft Defender ATP now in public preview [EN]
Web content filtering is a new feature in Microsoft Defender ATP that enables security administrators to track and regulate access to websites based on specified content categories. You can configure policies within Microsoft Defender Security Center to block or gather access data on certain categories across your machine groups.
This feature provides the following capabilities:
- Users are prevented from accessing websites in blocked categories, whether they are browsing on-premises or away
- Conveniently deploy varied policies to various sets of users using the machine groups defined in the Microsoft Defender ATP role-based access control settings
- Access web reports in the same central location, with visibility over actual blocks and web usage
- Support for most major web browsers, with blocks performed by SmartScreen and Network Protection.
Prerequisites
- Windows 10 Enterprise E5 license
- Access to Microsoft Defender Security Center portal
- Machines running Windows 10 Anniversary Update (version 1607) or later with the latest MoCAMP update (for Network Protection on Internet Explorer, Edge, Chrome, or Firefox)
- Machines running Windows 10 May 2019 Update (version 1903) or later (for a better user experience from SmartScreen on Edge). Note that if SmartScreen is not turned on, Network Protection will take over the blocking
- A valid license with a partner data provider (Cyren for example)
Integration
From the left-hand navigation menu in the MDATP portal, select Settings > General > Advanced Features. Scroll down until you see the entry for Web content filtering. Switch the toggle to On and Save preferences.
Configure web content filtering policies
Web content filtering policies specify which site categories are blocked on which machine groups. To manage the policies, go to Settings > Rules > Web content filtering.
Use the filter to locate policies that contain certain blocked categories or are applied to specific machine groups.
Create a policy
To add a new policy:
- Select Add policy on the Web content filtering page in Settings.
- Specify a name.
- Select the categories to block. Use the expand icon to fully expand each parent category and select specific web content categories.
- Specify the policy scope. Select the machine groups to specify where to apply the policy. Only machines in the selected machine groups will be prevented from accessing websites in the selected categories.
- Review the summary and save the policy. The policy may take up to 15 minutes to apply to your selected machines.
Reports
Select Reports > Web protection to view cards with information about web content filtering and web threat protection.
The following cards provide summary information about web content filtering :
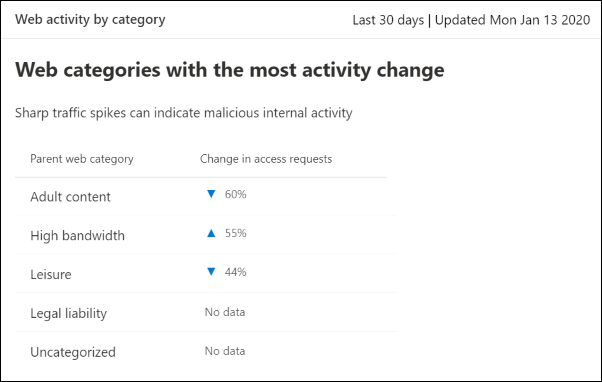
Web activity by category
This card lists the parent web content categories with the largest percentage change in the number of access attempts, whether they have increased or decreased (for the last 30 days, 3 months, or 6 months).
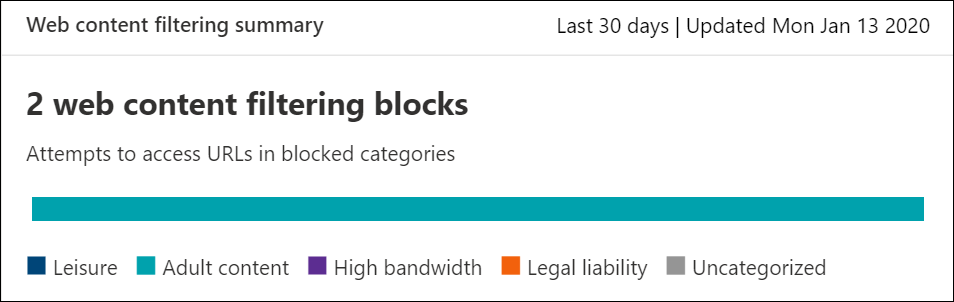
Web content filtering summary card
This card displays the distribution of blocked access attempts across the different parent web content categories.
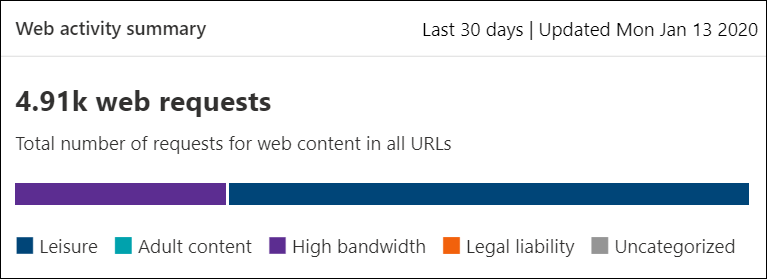
Web activity summary card
This card displays the total number of requests for web content in all URLs.
View card details
You can access the Report details for each card by selecting a table row or colored bar from the chart in the card. The report details page for each card contains extensive statistical data about web content categories, website domains, and machine groups.
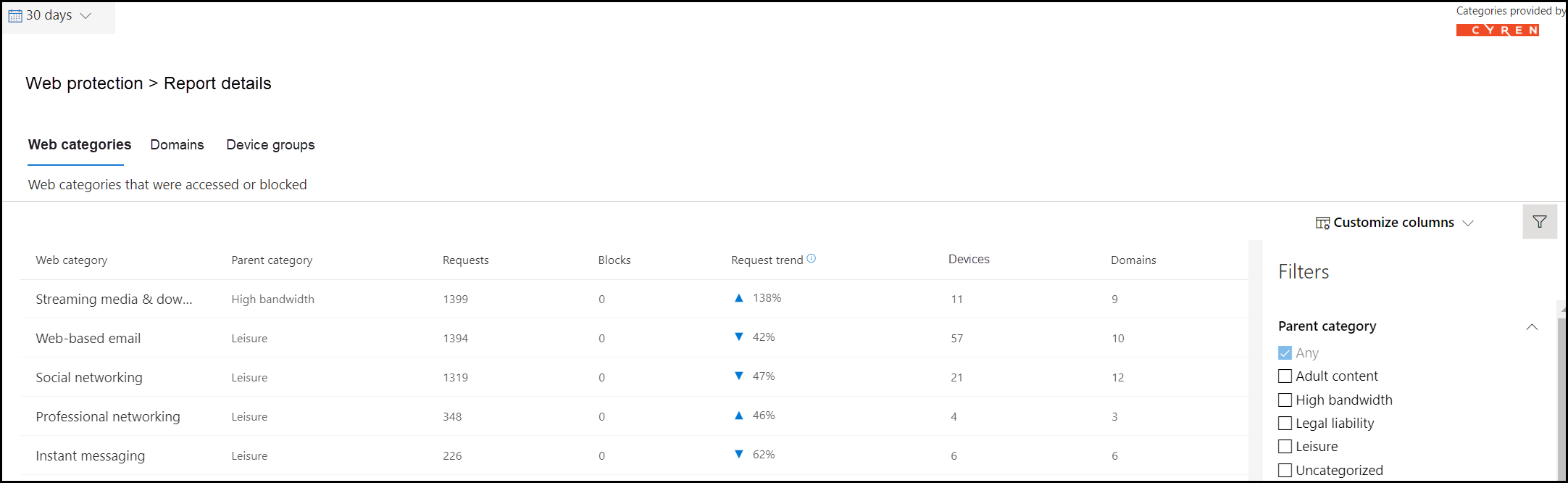
- Web categories: Lists the web content categories that have had access attempts in your organization. Select a specific category to open a summary flyout.
- Domains: Lists the web domains that have been accessed or blocked in your organization. Select a specific domain to view detailed information about that domain.
- Machine groups: Lists all the machine groups that have generated web activity in your organization
Note
For instance, you could set a policy to block ‘adult content sites’ across all of your machine groups, and create a separate policy to block ‘high bandwidth sites’ on just a few machine groups. Any category that is not being blocked will still have access information collected from them that you can view in the reports.

No Comments