Announcement – Microsoft Threat Protection enhancements [Public Preview]
Today, Microsoft is announcing public preview for three exciting enhancements:
- MTP Incident and Hunting APIs
- New MTP SIEM connectors for Splunk Enterprise and Micro Focus ArcSight
- MTP alerts will be available soon via the Microsoft Graph Security API
Microsoft Threat protection APIs
The Incidents API - This API exposes Microsoft Threat Protection incidents. You can pull all the alerts related to the incident and other information about them such as severity, entities that were involved in the alert, the source of the alerts (Azure ATP, Microsoft Defender ATP , Office 365 ATP) and the reason they were linked together.
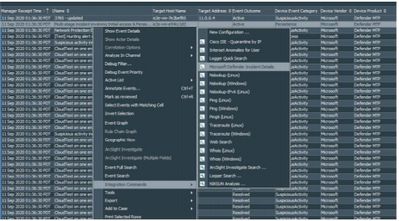
Cross-product threat hunting API– This API provides query-based access to Microsoft Threat Protection raw data store, aggregated across the suite protection products. Using the hunting API security teams can leverage their unique organizational knowledge and expertise to hunt for signs of compromise by creating their own custom queries.
Microsoft Threat protection SIEM connectors
- Security incidents and related evidence ingested through an add-on are mapped to the Splunk Common Information Model.
- Micro Focus ArcSight develops a new ArcSight FlexConnector that allows customers to integrate security incident in to Arcsight.
- A Microsoft Azure Sentinel connector will be coming soon.
- Waiting for it, you can integrate MTP through Logic App and Graph API
Microsoft Threat Protection alerts via the Microsoft Graph Security API
The Microsoft Graph Security API will provide a programmatic interface to connect multiple Microsoft security solution. Microsoft Threat Protection alerts and custom detection created by the customer will be surfaced under the Microsoft Graph Security Alert API in the coming weeks.


No Comments