Public preview of Microsoft Defender ATP web content filtering do not require additional licences anymore
There are an update from my previous article on Web Content Filtering. Indeed, it is now included as part of your Microsoft Defender ATP subscription – no additional licenses or costs, no additional partner license needed anymore.
Until the announcement of the 6th July, you needed an active 60-day trial subscription with a partner license in order to use Web Content Filtering with Microsoft Defender ATP.
The feature will permit to set access policies based on device groups, monitor and block certain online tools, and certain websites. It supports all browsers including Microsoft Edge through SmartScreen, Firefox, and Chrome through Network Protection.
Prerequisites
- Windows 10 Enterprise E5 license OR Microsoft 365 E3 + Microsoft 365 E5 Security add-on.
- Access to Microsoft Defender Security Center portal
- Devices running Windows 10 Anniversary Update (version 1607) or later with the latest MoCAMP update.
If Windows Defender SmartScreen is not turned on, Network Protection will take over the blocking. It requires enabling Network Protection on the device.
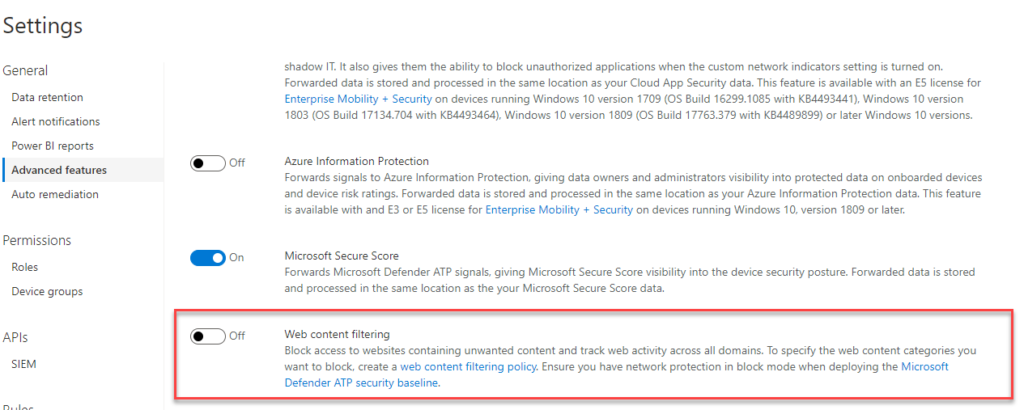
Turn on the feature
- Go to Settings > General > Advanced Features.
- Scroll down until you see the entry for Web content filtering.
- Switch the toggle to On and Save preferences.
Create a policy
To specify the web content categories you want to block, you have to create a web content filtering policy :
- Select Add policy on the Web content filtering page in Settings.
- Specify a name.
- Select the categories to block. Use the expand icon to fully expand each parent category and select specific web content categories.
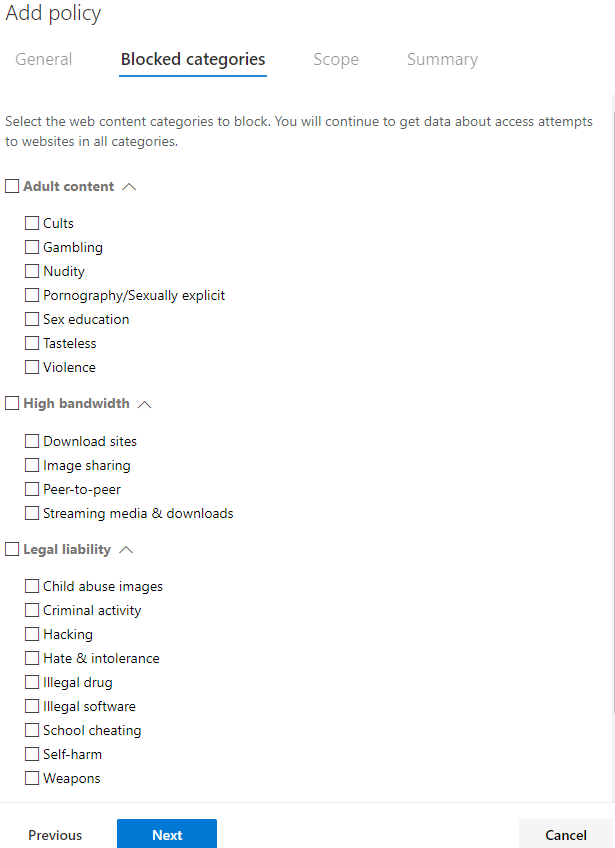
- Specify the policy scope. Select the device groups to specify where to apply the policy. Only devices in the selected device groups will be prevented from accessing websites in the selected categories.
- Review the summary and save the policy. The policy may take up to 15 minutes to apply to your selected devices.
Create an audit-only policy
You can deploy a policy without selecting any category on a device group. This action will create an audit only policy, to help you understand user behavior before creating a block policy.
Limitations and known issues in this preview
- Only Edge is supported if your device’s OS configuration is Server (cmd > Systeminfo > OS Configuration). This is because Network Protection is only supported in Inspect mode on Server devices, which is responsible for securing traffic across Chrome/Firefox.
- Unassigned devices will have incorrect data shown within the report. In the Report details > Device groups pivot, you may see a row with a blank Device Group field. This group contains your unassigned devices in the interim before they get put into your specified group. The report for this row may not contain an accurate count of devices or access counts.
Source
https://techcommunity.microsoft.com/t5/microsoft-defender-atp/an-update-on-web-content-filtering/ba-p/1505445
https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/web-content-filtering

No Comments