Windows Hello for Business Hybrid Cloud Kerberos Trust [General Availability]
Microsoft is excited to announce the general availability of hybrid cloud Kerberos trust, a new Windows Hello for Business deployment model that enables a passwordless sign-in experience.
Why passwordless and Windows Hello for Business?
Windows Hello for Business is a modern, strong, two-factor authentication method that is a more secure alternative to passwords and has been a native feature of the Windows operating system since Windows 10. It uses key-based or certificate-based authentication and at least two unique factors: something the user knows (PIN) or something the user is (biometrics), combined with something they have (physical access to their device). Taken together, Windows Hello for Business offers secure, convenient single sign-on to the device and cloud services.
Why hybrid cloud Kerberos trust?
This trust model enables you to deploy Windows Hello for Business using the infrastructure already introduced for supporting security key sign-in on Hybrid Azure AD-joined devices and on-premises resource access on…. Hybrid cloud Kerberos trust reduces any additional deployment requirements. This deployment is for hybrid and Azure AD joined enterprises who do not want to issue end-user certificates and have deployed 2016 domain controllers in each site to support authentication. It is simpler to deploy than key trust and does not require Active Directory Certificate Services.
How does it work?
Hybrid cloud Kerberos trust uses Azure AD Kerberos to address the complications of the key trust deployment model. Here is how it works in a simplified manner:
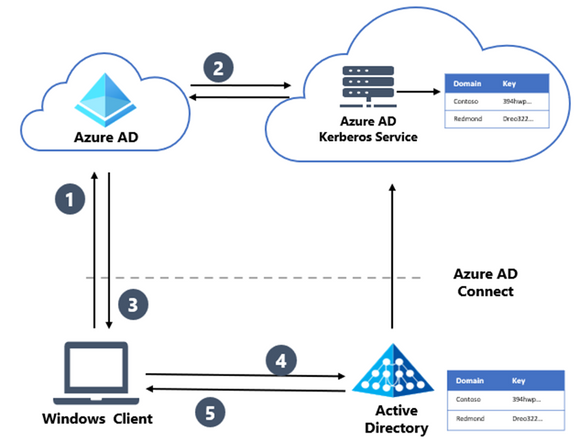
- The users sign in to Windows with Windows Hello for Business by authenticating with Azure AD.
- Azure AD checks for a Kerberos server key matching user’s on-premises AD domain and generates a partial Kerberos ticket granting ticket (TGT) for on-premises domain. The partial TGT contains the user security identifier (SID) only and no authorization data, such as groups.
- The partial TGT is returned to the client along with Azure AD Primary Refresh Token (PRT).
- Client contacts on-premises AD domain controller and exchanges the partial TGT for a full TGT. This is the same protocol flow used today for Read Only Domain Controller scenarios.
- Client has the Azure AD PRT and a full Active Directory TGT.
Essentially, we now can obtain a partial TGT from Azure AD, and subsequently exchange that for a full TGT in Active Directory. Because of this crucial piece, we no longer need to wait for Azure AD Connect to inform AD of the user’s public key. Users will authenticate directly with Azure AD with instant access to on-premises resources.
Moving to passwordless authentication
Microsoft recommends moving your organization to a passwordless authentication model to help protect your employees from password attacks, such as phishing. Windows Hello for Business is available by default on Windows 11 devices and hybrid cloud Kerberos trust deployment is the simplest deployment model, as it offers:
- No PKI requirements
- No Azure AD Connect synchronization dependency for writing back the public keys to Active Directory
- No device write-back requirement (only applicable for certificate trust deployments)
- No Active Directory Federation Services (AD FS) deployment requirement (only applicable for certificate trust deployments)
Organizations can take advantage of this Windows Hello for Business deployment model and deploy passwordless credentials with minimal additional setup or infrastructure. Hybrid cloud Kerberos trust is the new recommended method of deployment when certificates are not needed, replacing the key trust method as the default recommendation.
Source
Windows Hello for Business Hybrid Cloud Kerberos Trust is now available! – Microsoft Community Hub

No Comments